Sqlmap – is one of the most popular open source tool for automated SQL Injection scanning and exploitation and it is very popular among security specialists and pentesters. It works not only with SQL Injections, but also with XSS. What makes sqlmap different from other utilities to detect SQL injections, so this is an opportunity to exploit each found vulnerability.
Two people are engaged in the development of the scanner. Miroslaw Štampar (@stamparm), a professional software developer from Croatia, and Bernardo Damele (@inquisb), INFORMATION SECURITY consultant from Italy, now living and working in the UK. The project came to light in 2006, thanks to Daniel Bellucci (@belch), but truly began to develop rapidly after 2009, the work involved Miroslaw and Bernardo.
What is SQL Injection?
SQL injection is an attack on the Web application in which need to construct the SQL statement from user input by a simple concating (for example, $query = “SELECT * FROM users WHERE id =”. $ _REQUEST [“id”]). In case of success, an attacker can change the SQL query execution logic as he needs. Most often, it performs a simple fingerprinting DATABASE, and retrieves the tables with the most ‘ interesting ‘ names (such as “users”).
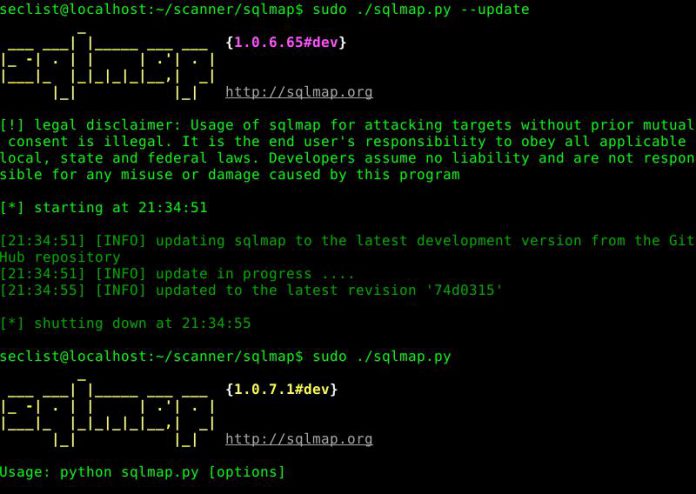
The most simple way to launch sqlmap for scanning is:
./sqlmap.py -u target
Such way it will execute scanning of all available GET and POST parameters on the websites.
If you already have direct link for example with GET request with 5 threads, you can use following command:
./sqlmap.py -u target.url/something?id=123 --threads=5 --dbs
In case if you want to do testing with GET request, changing user-agent, using maximum possible threads and also you have acknowledge of database:
./sqlmap.py -u target.url/something?id=123 --threads=10 --dbms=MySQL --random-agent --level=3 --risk=1 --batch --dbs
You can use and change commands and parameters as you need on current task. Sqlmap can work with proxies, TOR, change user-agents, use many type of parameters for information retrieval from database or even create sql-shell.
Automated audit with sqlmap on OWASP


























Thanks for the good interesting article, good read as always.
Nice blog! Is your theme custom made or did you download it from somewhere? A theme like yours with a few simple tweeks would really make my blog stand out. Please let me know where you got your theme. Thank you
I believe this is among the most vital information for me. And i am happy studying your article. However want to observation on some basic things, The site style is perfect, the articles is actually nice : D. Good task, cheers
Really enjoyed this post, can I set it up so I get an update sent in an email when you publish a new update?
I just want to say I am newbie to blogging and site-building and seriously enjoyed your web site. Likely I’m likely to bookmark your website . You definitely come with perfect well written articles. Thanks for sharing your blog site.
Comments are closed.